The PCICSO, Protection of Critical Infrastructures (Computer Systems) Ordinance, is a new framework introduced by the Hong Kong Government to strengthen the cybersecurity and resilience of CIOs (critical infrastructure operators). Effective since January 2026, the ordinance establishes statutory obligations for CIOs to protect their computer systems against cyberthreats, proactively manage risks, and respond effectively to cybersecurity incidents. This regulation makes it clear that operators of critical infrastructures are now expected to demonstrate strict, enforceable controls over how systems, devices, and data are handled.
Protection of Critical Infrastructures (Computer Systems) Ordinance (PCICSO)
The PCICSO regulatory framework is structured around three core obligations to provide CIOs with a comprehensive and systematic approach for cyber risk management. CIOs are defined as organizations designated by the regulatory authority based on their dependence on core operations of computer systems, the sensitivity of controlled data, the level of operational and management control over the infrastructure, and the information supplied for compliance.
The three core obligations that CIOs are required to comply with are:
- Organizational: Governance and organizational requirements to ensure clear accountability, policies, and oversight for cybersecurity.
- Preventive: Preventive and protective measures, requiring operators to implement appropriate technical and operational safeguards to secure critical computer systems.
- Incident Reporting and Response: Capabilities to mandate timely detection, handling, and notification of significant cybersecurity incidents.
Key Highlights
While the ordinance covers a broad range of requirements, there are a few key takeaways that CIOs should keep in mind. According to Schedule 3, Part 1 of the ordinance, operators are required to have policies in place to:
- Identify, assess, monitor, mitigate, and respond to risks relating to computer system security and system vulnerabilities
- Control access to critical computer systems
- Manage suppliers of computer-related services and products adopted for the systems
Industry-Leading Solutions to Aid Compliance
Device and Endpoint Compliance as a Foundation
Endpoint security posture and vulnerability management are highly emphasized in the PCICSO guidelines, requiring vulnerabilities to be detected, assessed, and remediated in a timely manner. Only compliant devices should be permitted to interact with critical systems, while endpoints with missing patches, outdated software, or security risks must be blocked or restricted until remediated. MetaDefender Endpoint™ supports compliance with these requirements by enforcing device compliance before access is granted and evaluating each endpoint against organizational policies. This evaluation includes vulnerability and patching status, ensuring only devices meeting the required security posture can connect.
In addition, MetaDefender Endpoint enables vulnerability and patch management across endpoints, covering operating systems and third-party applications. It actively detects vulnerabilities, remediates risks, and provides recommended fixes, with patching support for 1,100+ applications. For auditable compliance enforcement and incident investigations, all endpoint security and compliance status can be centrally monitored and audited through My OPSWAT™ Central Management.

Mitigating Removable Media Risks
Access control is one of the key focus areas under the ordinance. This increases the need for CIOs to carefully govern all access pathways to critical systems, including removable media.
The use of USB drives and other portable media remains common in operational environments, especially where networks are segmented or isolated, making them a high-risk attack vector in the OT/ICS environments. According to SANS 2025 OT/ICS Budget Report, 15.2% of the attack vectors came from compromised removable media.

To mitigate these risks, OPSWAT helps organizations prevent removable media risks with:
- Removable Media Threat Mitigation at the Point of Entry: MetaDefender Kiosk™ secures data flows into critical environments by scanning and sanitizing removable media at the point of entry. It was recognized as part of Emerson's DeltaV Silver Alliance, proving its effectiveness in multiple environments and use cases.
- Pre-Run Endpoint Protection and Device Control: MetaDefender Endpoint™ provides advanced endpoint protection for operational environments by actively scanning removable media upon insertion and ensuring that only clean devices or content can be accessed within critical systems.
- Media Validation as an Extra Layer of Defense: MetaDefender Endpoint Validation and MetaDefender Media Firewall™ provide an additional layer of security by enforcing scanning and sanitization policies.
- Centralized Protection Monitoring: Through My OPSWAT™ Central Management, MetaDefender Endpoint™ and MetaDefender Kiosk™ support centralized policy enforcement to control device access, monitoring and managing portable media usage, and activity logging.
Governing Contractor and Supply Chain Device Access and Secure File Storage
Since critical infrastructure cannot operate in total isolation, daily operations often require granting network access to external devices brought in by vendors, contractors, and partners. Transient devices, such as third-party laptops and replacement workstations, can bypass proper screening due to time pressure or insufficient verification tools, creating potential initial attack vectors.
Recent industry data from the SANS 2025 ICS/OT and IBM’s 2025 Cost of a Data Breach reports revealed that:
- Transient device attacks surged by 221%
- 27.3% of all OT incidents originated from transient devices
- Third-party and supply-chain compromises average about $4.9 million per breach
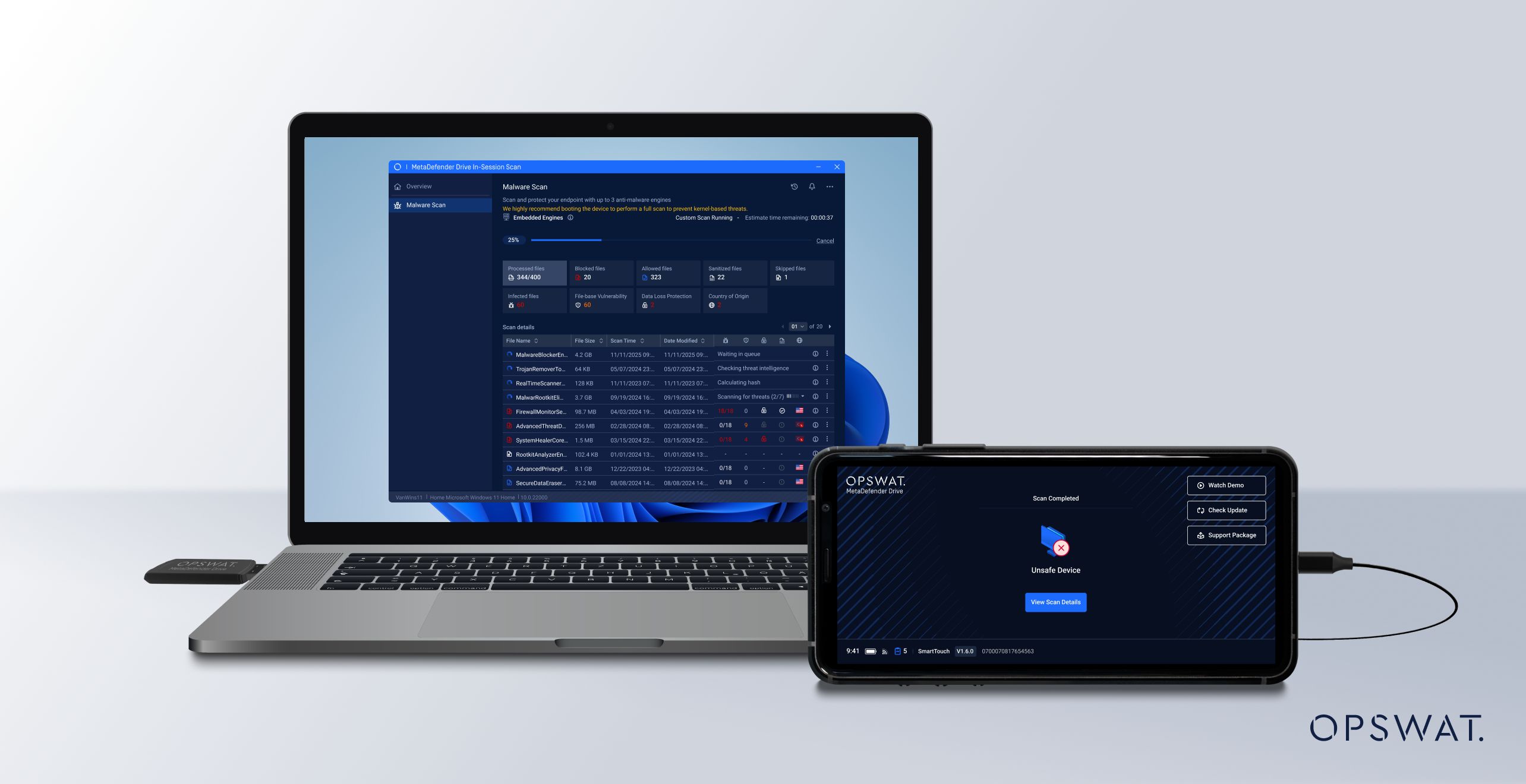
MetaDefender Drive is designed to address these issues by scanning and verifying transient devices before granting them access to your critical networks. Through secure pre-boot scanning, operators can inspect devices beyond the host operating system to detect hidden threats before network entry.
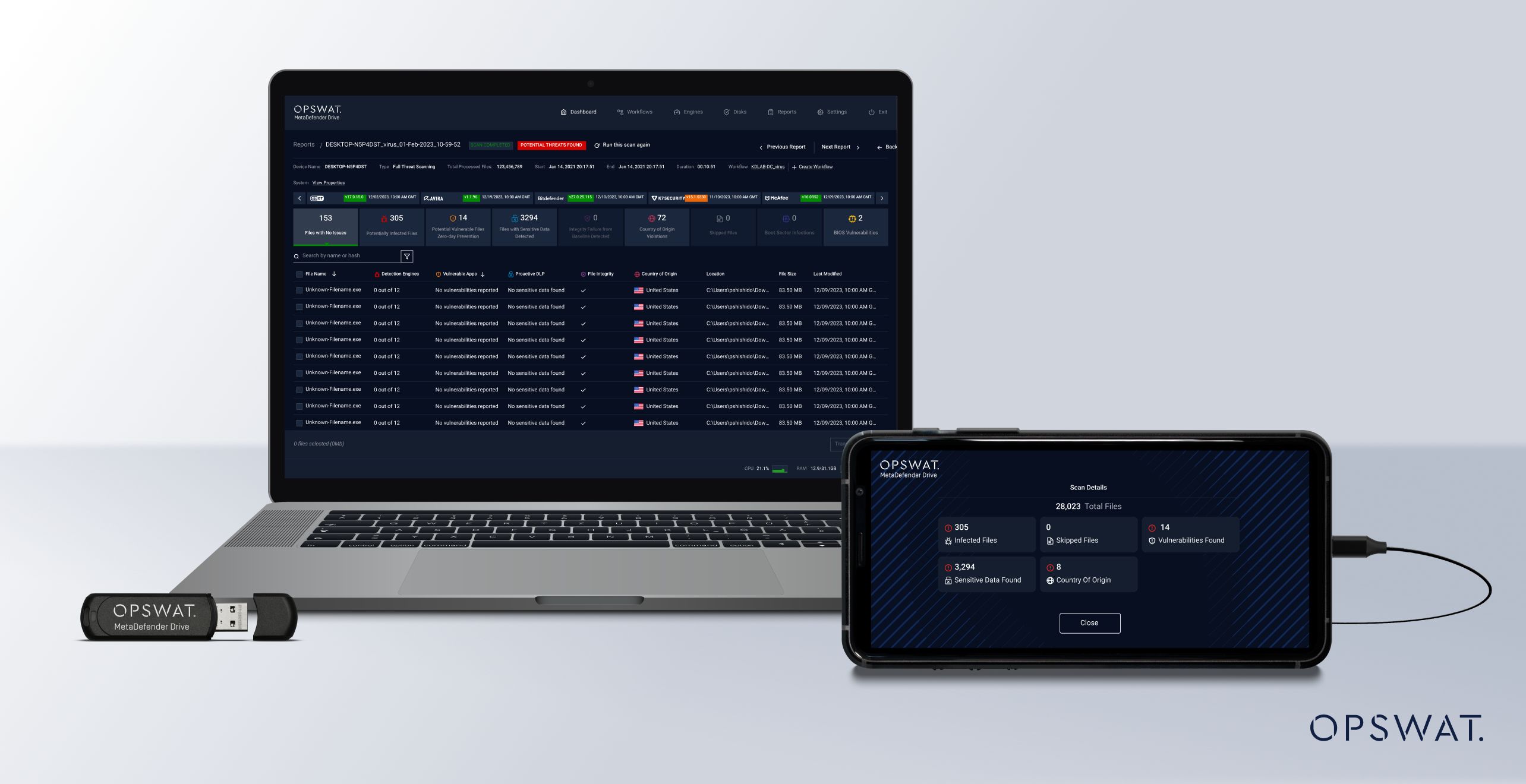
For critical systems that cannot be powered down due to operational constraint, MetaDefender Drive also supports in-session scanning, enabling device inspection while the operating system is running, enabling deep inspection in critical environments where downtime is unacceptable.
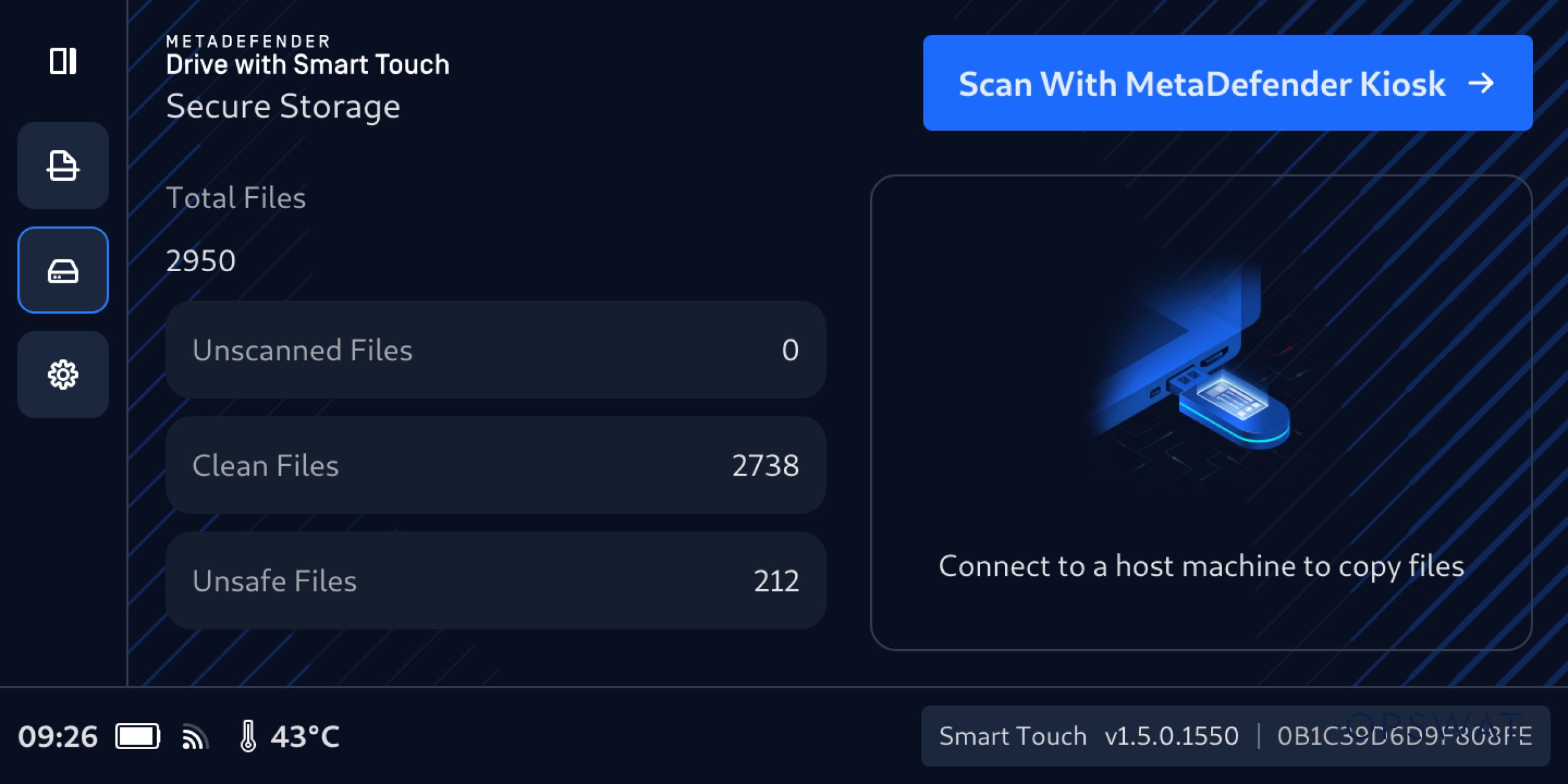
Additionally, MetaDefender Drive with Smart Touch enables secure file storage by storing data, similar to a standard USB drive, while keeping unscanned files hidden, allowing only scanned files to be shared or distributed.
Network Segmentation and One-Way Data Flow
Beyond logical segmentation, PCICSO recognizes that certain critical systems require stronger guarantees than software-based controls provide. Firewalls, ACLs, and segmentation policies remain vulnerable to misconfiguration, credential abuse, and zero-day exploits. For high-impact systems where availability and integrity are crucial, physically enforcing trust boundaries is a decisive control.
MetaDefender NetWall™ addresses this requirement through hardware-enforced unidirectional data flow to ensure data can move out of critical environments for monitoring, analytics, and compliance reporting, while preventing inbound communication. Unlike conventional network controls that rely on policy enforcement, this approach eliminates entire classes of attack vectors by design. It prevents malware, remote commands, and lateral movement from traversing back into protected systems, supporting PCICSO’s emphasis on reducing systemic risk and limiting exposure pathways to critical systems.
From an operational perspective, MetaDefender NetWall™ enables CIOs to meet monitoring, logging, and reporting obligations without compromising system isolation. Logs, telemetry, and operational metrics can be safely transmitted to IT or SOC environments for centralized analysis, while OT and control systems remain intact, supporting alignment with the ordinance.

From Compliance to Resilience
Applying the new Hong Kong cybersecurity ordinance guidelines helps organizations enforce device compliance, control file movement, manage removable media, and segment networks. As critical infrastructure becomes more connected while still relying on disruption-intolerant systems, security controls must operate without interrupting operations.
The OPSWAT platform unifies these capabilities across endpoints, removable media, transient devices, and data flows, addressing common entry points while delivering the visibility regulators expect. To learn more about how OPSWAT helps critical infrastructure organizations meet these requirements and strengthen cyber resilience, talk to one of our experts today.

