Australia’s SOCI (Security of Critical Infrastructure) Act has reshaped how responsible entities manage cyber and operational risk. The Act shifts the focus from high-level policy alignment to demonstrable, operational resilience supported by evidenced risk management practices.
The latest amendments reinforce the Australian Government’s expectation that critical infrastructure owners move beyond static frameworks toward practical, operational controls, particularly in cyber and information security.
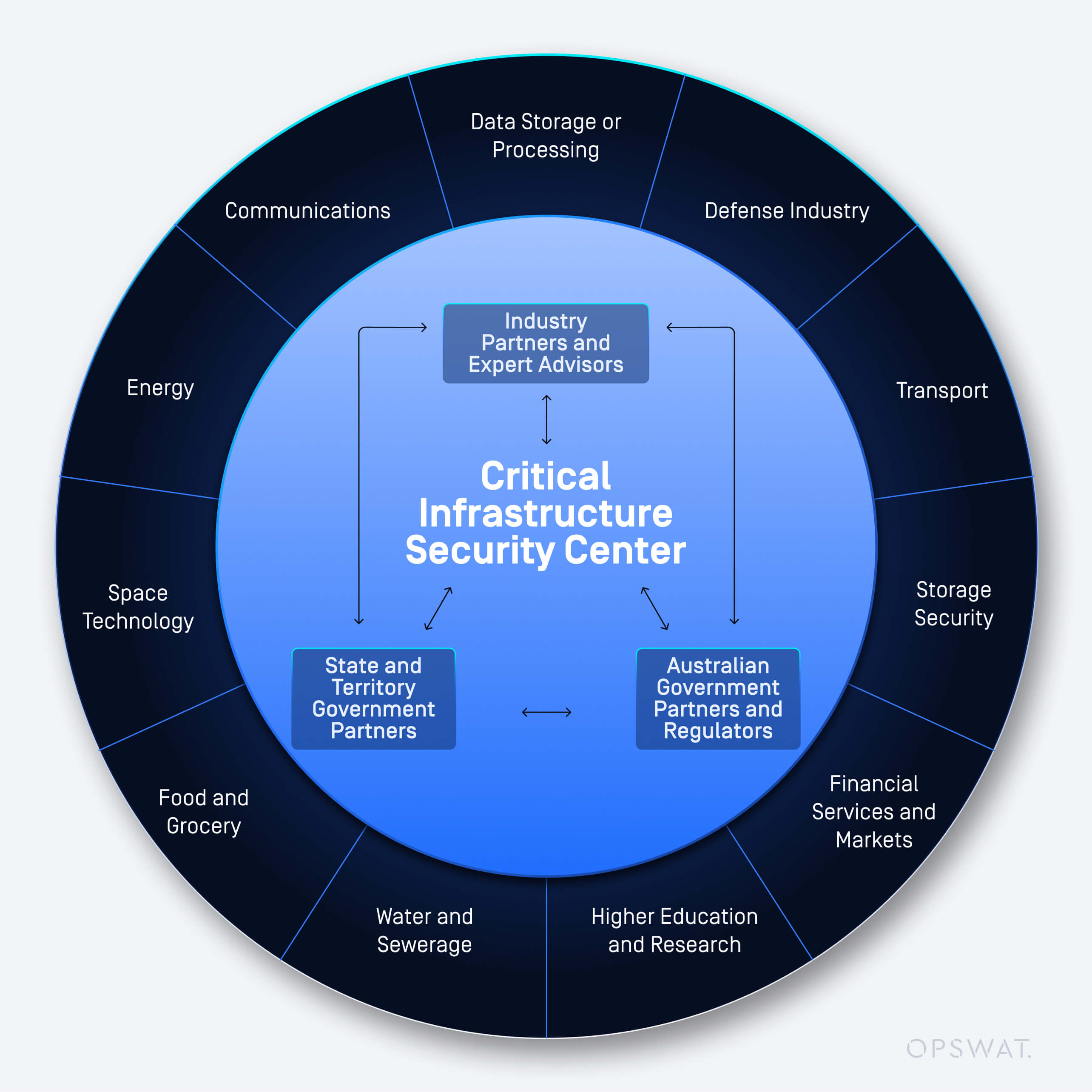
Under Part 2A of the SOCI Act, responsible entities must establish, maintain, and comply with the CIRMP (Critical Infrastructure Risk Management Program). This requirement applies across sectors including:
|
|
|
Most of these sectors are required to adopt a more mature, demonstrable, and continuously improving approach to managing risk across people, processes, and technology.
Amendments introduced between 2021 and 2024 reinforce three key expectations:
- Clearly defined and implemented cyber and information security controls
- Continuous risk assessment and review, not static documentation
- Board-level oversight and accountability
Regulators now expect organizations to demonstrate the effectiveness of controls, supported by monitoring, logging, and governance artefacts, as well as their operational effectiveness. Compliance is no longer a documentation exercise. It is an operational and executive responsibility tied directly to national resilience.
The SOCI Act and the CIRMP
Responsible entities must establish, maintain, and comply with a CIRMP that is proportionate to the asset’s criticality and threat environment. The CIRMP must move beyond policy statements and demonstrate practical, risk-based controls that address real-world hazards.
Under CIRMP requirements, organizations must:
- Identify hazards that could materially impact critical infrastructure assets
- Minimize or eliminate material risks arising from those hazards
- Regularly review and update controls to reflect changes in threat activity
- Maintain records and evidence to support regulatory assurance and engagement
- Address risks across four defined hazard vectors:
- Cyber and information security hazards
- Physical security and natural hazards
- Personnel hazards
- Supply chain hazards
Although CIRMP remains principle-based, regulators expect operational maturity. Organizations must show that controls are implemented, monitored, and continuously improved. Documentation alone is not sufficient. Evidence of governance oversight, risk assessment processes, and technical enforcement mechanisms is required.
Cyber Risk as a Core Focus of the CIRMP
Cyber and information security hazards represent one of the most significant and rapidly evolving risks to critical infrastructure. The CIRMP reinforces cyber risk as a central pillar of resilience planning, reflecting the increasing frequency of ransomware, supply chain compromise, and attacks targeting OT environments.
Responsible entities must demonstrate a clear understanding of how cyberthreats could materially impact the availability, integrity, or reliability of critical infrastructure assets.
This includes the ability to identify:
- How data, files, and software enter and move through IT, OT, and ICS environments
- Where trust boundaries exist between IT, OT, and third-party networks
- How malware or unauthorized access could propagate into operational systems
- Whether vendors, contractors, or portable media introduce unmanaged risk
The SOCI Act amendments make clear that legacy systems, air-gapped networks, and constrained OT environments are not exempt from cyber risk obligations. Organizations must adapt controls to suit these environments rather than avoid implementing them.
In practice, this requires visibility and enforceable control at commonly exploited entry points, including:
- File uploads and downloads
- Atașamente e-mail
- Managed and unmanaged endpoints
- Removable media
- Remote access pathways
- IT and OT convergence zones
Effective cyber risk management under CIRMP depends on preventative controls that reduce exposure before threats reach critical systems. Logging, monitoring, and evidence generation are essential to demonstrate that these controls operate as intended.
Aligning CIRMP Hazard Categories with Practical Control Implementation
The CIRMP requires organizations to address risk across four hazard vectors. Each vector requires enforceable, auditable controls that reduce material risk to critical infrastructure assets.
Hazard vectors include:
- Cyber and information security
- Personal
- Supply chain
- Physical security
The following sections outline how these hazard categories translate into operational security controls within critical infrastructure environments.
1. Cyber and Information Security Hazards
CIRMP requires organizations to implement controls that minimize material cyber risks capable of disrupting the availability, integrity, or reliability of critical infrastructure assets. Common cyberthreats include phishing, malware, ransomware, and denial-of-service attacks.
File-based threats remain one of the most common initial access vectors. Organizations must secure how files are uploaded, downloaded, transferred, and introduced into both IT and OT environments.
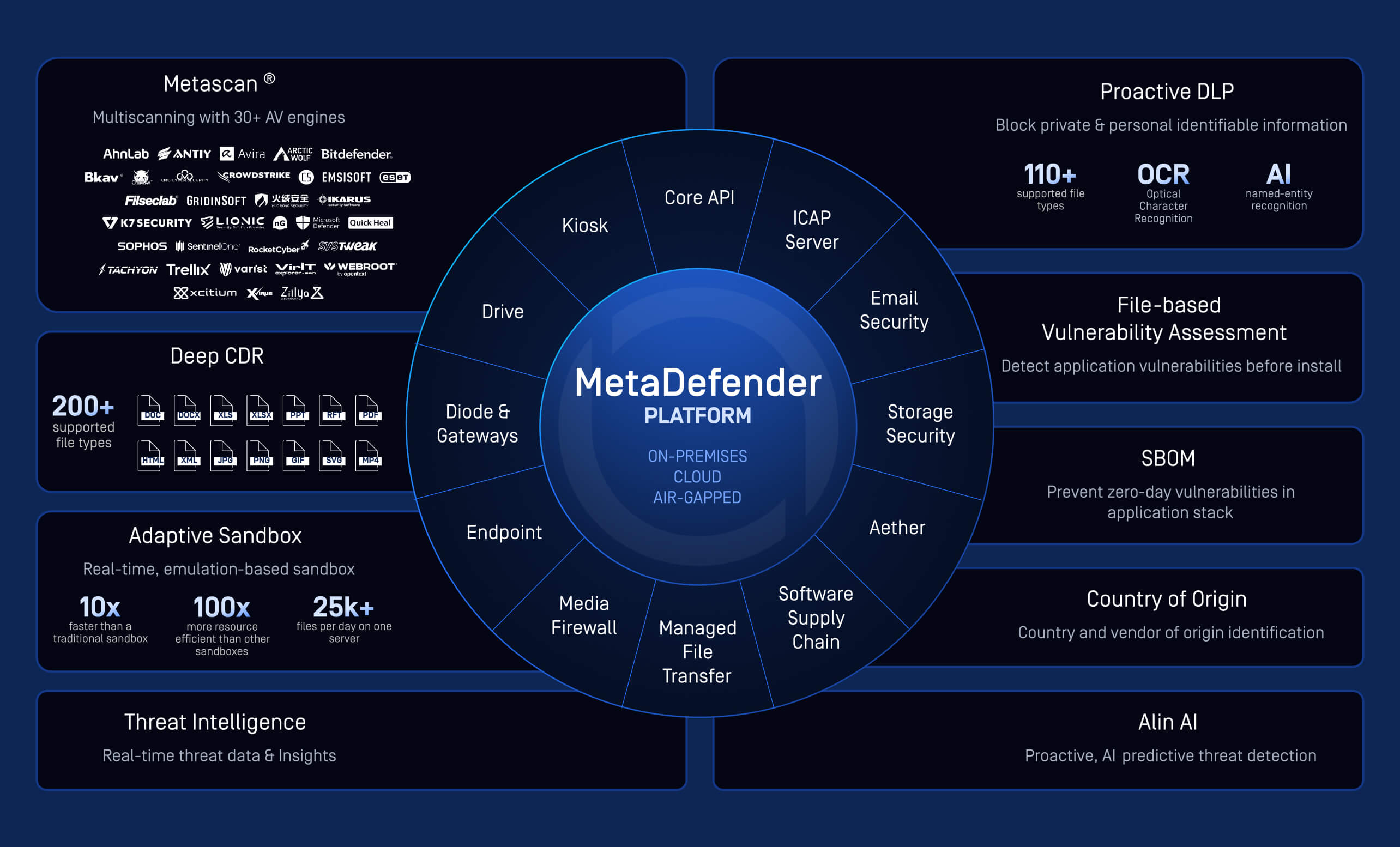
OPSWAT’s MetaDefender Core™ is designed to prevent file-borne threats before they reach users or critical systems. It integrates into existing infrastructure to inspect uploads, downloads, email attachments, and file transfers without disrupting operational workflows.
MetaDefender Core applies multiple detection technologies to support defense-in-depth inspection, including:
- Metascan™ multiscanning technology with more than 30 anti-malware engines
- Signature-based, heuristic, and machine learning-based detection
- AI-driven, machine learning-based pre-execution zero-day detection
- File reputation and hash analysis
For unknown and zero-day threats, Deep CDR™ Technology performs deep file sanitization to recursively remove embedded threats such as scripts, macros, and out-of-policy content, then regenerates safe and usable files while preserving business functionality.
Adaptive Sandbox™ analysis enables behavioral observation in a controlled environment. Proactive DLP™ inspects file content to detect sensitive information and enforce policy-based actions such as removing, redacting, or watermarking content before files are released to users or systems.
Additional inspection capabilities include:
- True file type verification
- Archive extraction and recursive scanning
- File-based vulnerability assessment
- Data loss prevention and content inspection
These capabilities support CIRMP objectives by:
- Reducing reliance on a single detection technology
- Detecting and preventing zero-day attacks
- Generating auditable evidence of due diligence in threat detection
2. Personnel Hazards
Under the CIRMP, personnel hazards include risks introduced by employees, contractors, subcontractors, interns, and other individuals with access to critical infrastructure assets. Organizations must assess who qualifies as a critical worker, what level of access they hold, and whether that access could introduce material risk.
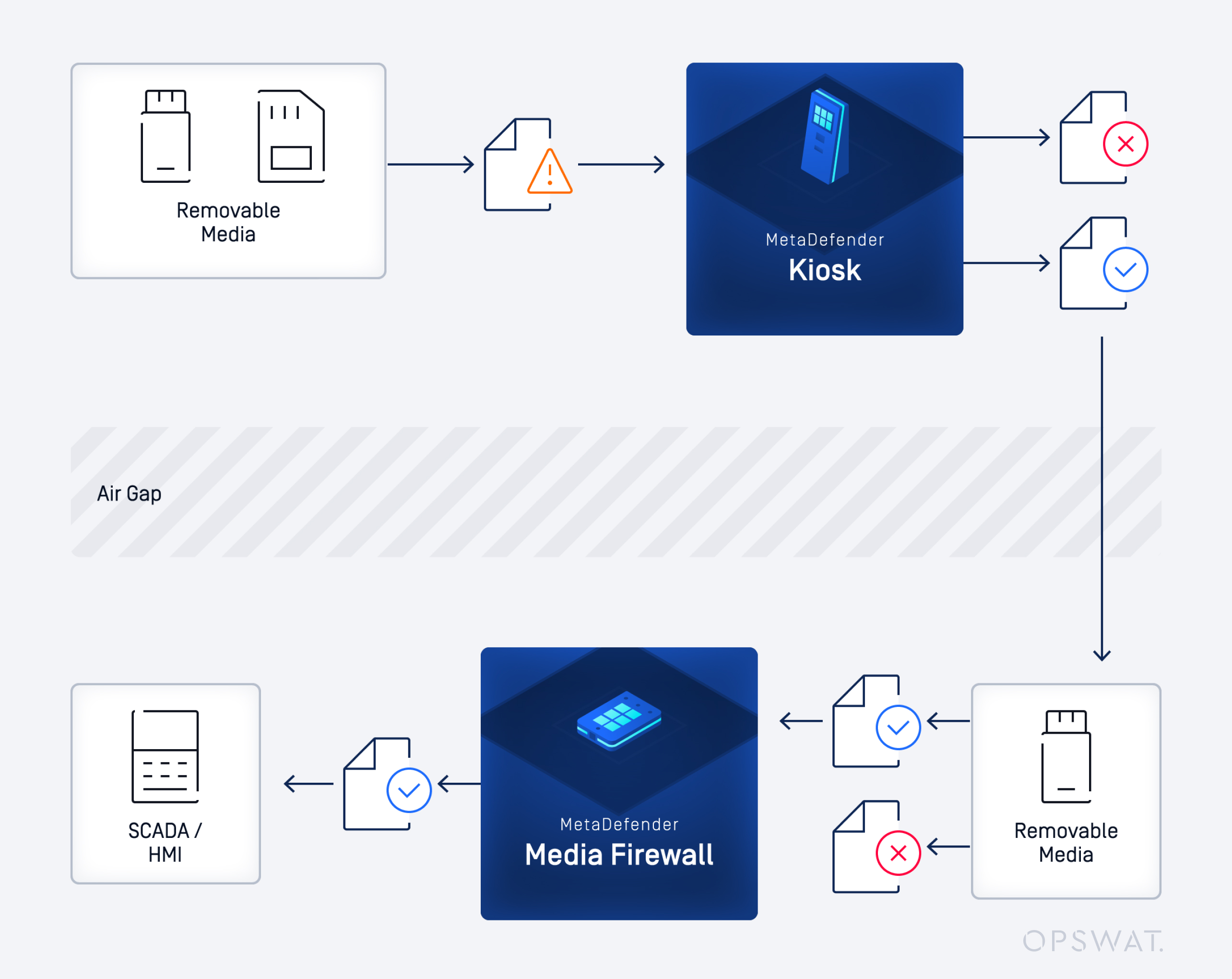
Removable media and portable devices remain common vectors for introducing malware into OT environments, particularly in air-gapped or segmented networks. Without enforceable controls, these pathways can bypass perimeter defenses.
MetaDefender Kiosk™ and MetaDefender Media Firewall™ are designed to enforce security controls at media entry points and at the HMI (Human Machine Interface) layer.
MetaDefender Kiosk automates the scanning and sanitization of removable media before files are allowed into secure environments. It enforces predefined security policies and generates logs to support audit requirements.
MetaDefender Media Firewall provides inline inspection and policy enforcement for data transfers between networks, including OT segments. It prevents unauthorized or unsafe files from moving into critical systems.
These controls support CIRMP personnel hazard requirements by:
- Reducing the risk of malicious or negligent insider activity
- Enforcing secure handling of removable media within OT networks
- Restricting the use of unapproved devices
- Improving visibility into who introduces files and when
3. Supply Chain Hazards
The SOCI Act explicitly identifies supply chain hazards as a material risk category under the CIRMP. Responsible entities must address risks introduced by vendors, contractors, OEMs (original equipment manufacturers), and third-party service providers.
Supply chain exposure can arise through:
- Third-party endpoints connecting to critical networks
- Remote access pathways into OT environments
- Portable devices brought onsite by contractors
- Software updates and maintenance activities
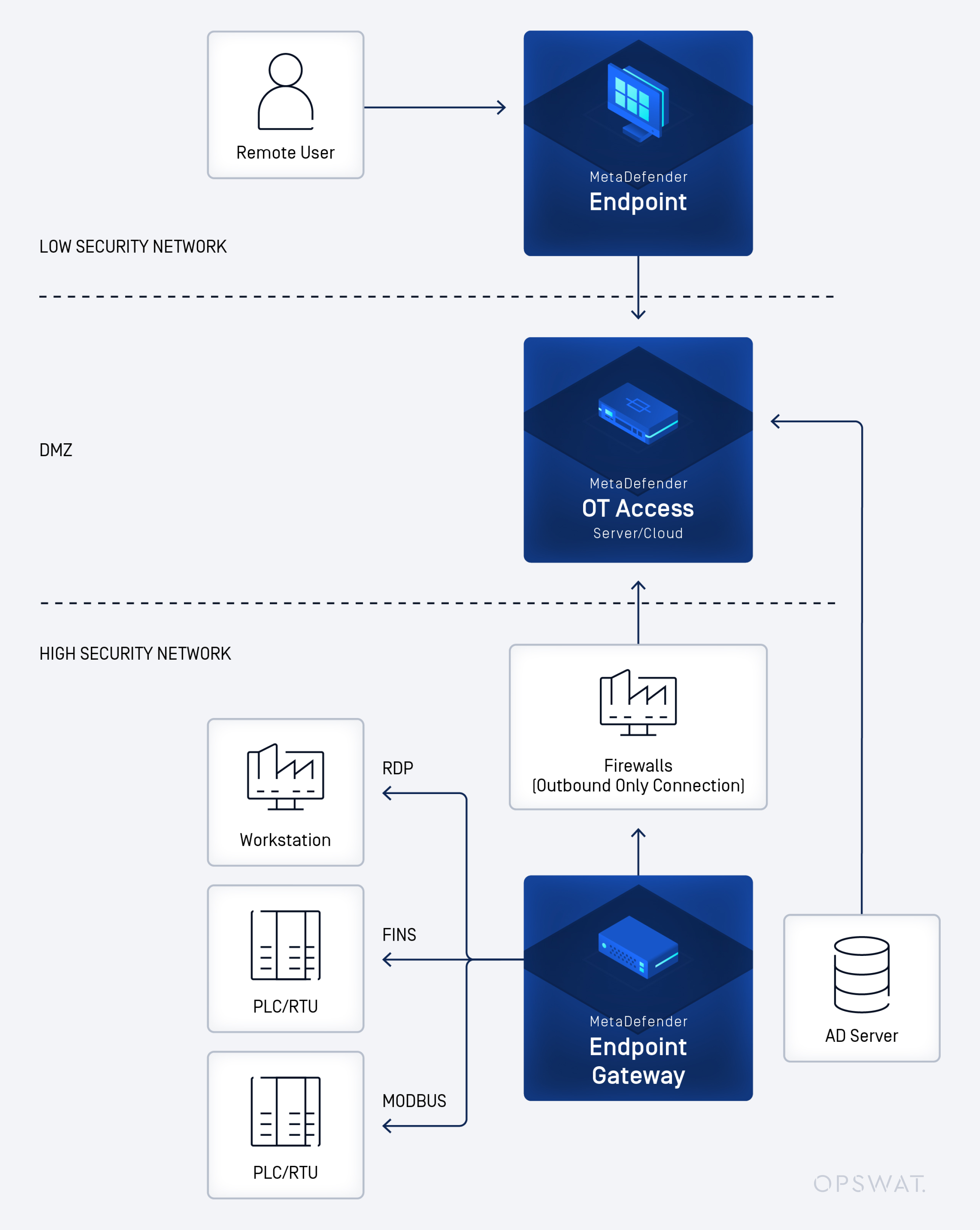
Many critical infrastructure operators rely on remote connectivity to monitor assets, perform diagnostics, and conduct upgrades across distributed or regional sites. Without appropriate controls, these access pathways can introduce cyberthreats into sensitive environments, including air-gapped or semi-connected OT networks.
OPSWAT MetaDefender Drive™ and MetaDefender OT Access™ are designed to reduce risk from third-party interactions with critical systems.
MetaDefender Drive scans and assesses transient laptops, desktops, and servers outside the host operating system before they connect to secure environments. It detects malware, identifies vulnerabilities, and validates device integrity to ensure only trusted systems are allowed into controlled or air-gapped networks.
MetaDefender OT Access is a secure remote access solution purpose-built for OT and CPS (Cyber-Physical Systems) environments. It enables controlled connectivity for third parties and remote personnel while enforcing granular access controls and session management policies.
These capabilities support CIRMP supply chain hazard requirements by:
- Protecting critical systems against interference or disruption introduced through third-party assets
- Restricting access to authorized systems and functions
- Improving visibility into vendor and contractor interactions with critical infrastructure
4. Physical Security and Network Segmentation Hazards
Physical and environmental hazards remain a core component of the CIRMP. In modern critical infrastructure environments, physical security increasingly intersects with cyber risk, particularly where OT systems rely on controlled data flows between IT and OT networks.
Many critical infrastructure environments operate legacy OT systems where traditional endpoint security tools cannot be deployed. As a result, security controls must be implemented at network boundaries and data transfer points.
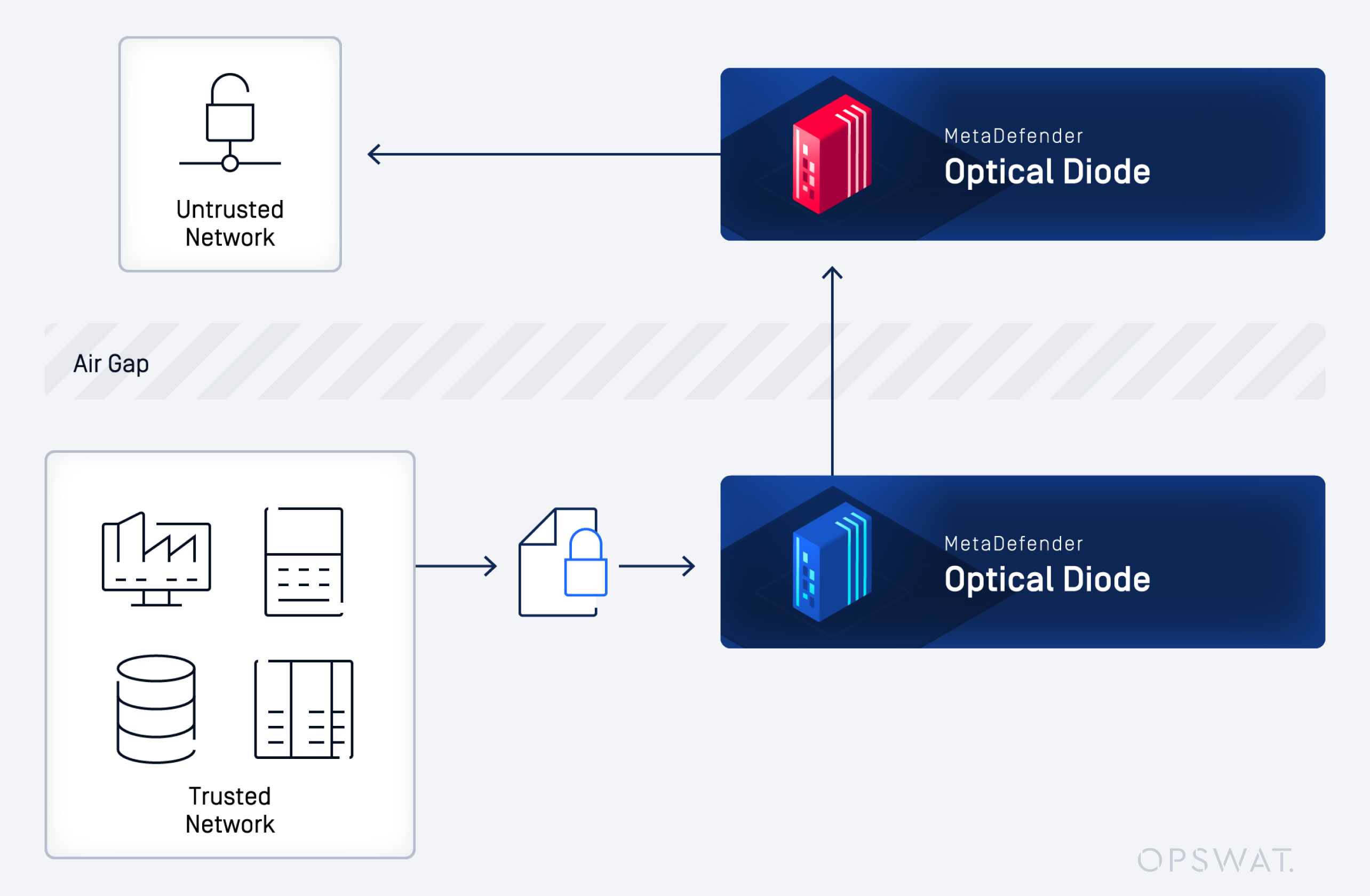
Regulatory guidance and industry standards commonly recommend the use of unidirectional gateways, also known as data diodes, to protect sensitive OT networks. These controls enforce one-way data flow to prevent unauthorized access, command injection, or data exfiltration from critical systems.
MetaDefender Netwall™ enforces hardware-based unidirectional data transfer. By physically preventing reverse traffic, it eliminates the risk of inbound network-based attacks across segmented environments.
When deployed within a DMZ (demilitarized zone) architecture and combined with layered firewall controls, this approach supports:
- Reduced risk of malware propagation between IT and OT networks
- Protection against unauthorized remote access into critical systems
- Preservation of operational continuity
- Demonstrable risk-aware network design aligned with CIRMP principles
By controlling how data moves between trust zones, organizations can strengthen both physical and cyber resilience in environments where availability and safety are critical.
From Regulatory Compliance to Operational Resilience
Australia’s SOCI Act and the CIRMP represent a measurable shift in regulatory expectations. Responsible entities must move beyond documented intent and demonstrate that risk controls are implemented and continuously improved in practice.
Regulators expect organizations to show that controls are:
- Appropriate for the asset’s criticality and threat profile
- Embedded into operational workflows
- Supported by logging, monitoring, and governance oversight
- Capable of withstanding board and regulatory scrutiny
CIRMP is not a static compliance framework. It requires preventative, enforceable, and auditable controls across cyber, personnel, supply chain, and physical hazard vectors.
Preventative security plays a central role in meeting these expectations. Controls must operate at common entry points, across IT, OT, and ICS boundaries, and within third-party interaction pathways. They must also generate the visibility and evidence required to support governance, assurance, and regulatory engagement.
OPSWAT’s focus on critical infrastructure protection directly supports the operational and regulatory demands of Australia’s SOCI Act. Implementing enforceable technical controls under CIRMP strengthens both compliance posture and real-world resilience.
In critical infrastructure environments, preventative security is not optional. It is foundational to maintain availability, safety, and public trust. To learn how to align your CIRMP strategy with enforceable preventative controls, speak with an OPSWAT cybersecurity expert.
Întrebări frecvente
What is the purpose of the CIRMP?
The CIRMP requires responsible entities under Australia’s SOCI Act to identify, assess, and manage risks that could materially impact critical infrastructure assets. It ensures organizations implement proportionate controls across cyber, personnel, supply chain, and physical hazard vectors.
Does CIRMP apply to OT environments?
Yes. CIRMP obligations apply to both IT and OT environments. Legacy or air-gapped systems are not exempt. Organizations must adapt controls to the realities of constrained OT systems.
What types of cyberthreats are most relevant to critical infrastructure?
Common cyberthreats include ransomware, phishing, file-borne malware, supply chain compromise, and unauthorized remote access. File transfers, removable media, and third-party connections are frequent entry points.
How can organizations demonstrate compliance with CIRMP cyber requirements?
Organizations must show that controls are implemented and effective. This includes maintaining logs, monitoring activity, enforcing technical policies, and providing documented governance oversight and review processes.
Why is preventative security emphasized under the SOCI Act?
The SOCI Act emphasizes minimizing material risk to critical infrastructure assets. Preventative controls reduce the likelihood that cyberthreats, insider risks, or supply chain exposures reach critical systems, supporting operational continuity and regulatory assurance.

